- NetWitness Community
- Discussions
- Re: Whitelist false positive in Endpoint ESA Rules
-
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Whitelist false positive in Endpoint ESA Rules
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2021-02-15 11:26 PM
We have a poorly coding internal application that keeps triggering the Endpoint ESA rule 'unsigned outbound from temp directory'
What would be the best way to whitelist this so it doesn't keep showing up in alerts in the respond module?
- Labels:
-
RSA NetWitness Endpoint
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2021-02-16 03:06 PM
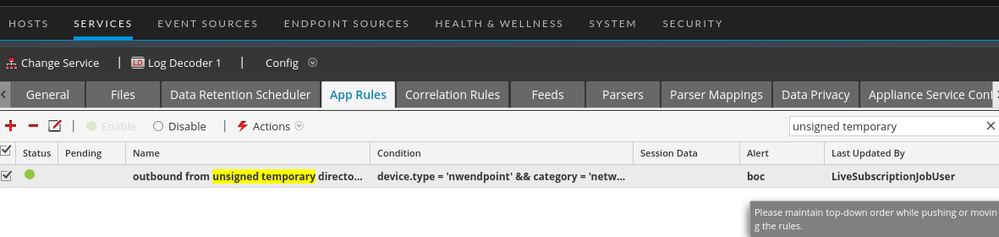
Your easiest and best option will be to adjust the companion App Rule that is the source of that ESA rule:
..and add the additional syntax to filter out your internal application.
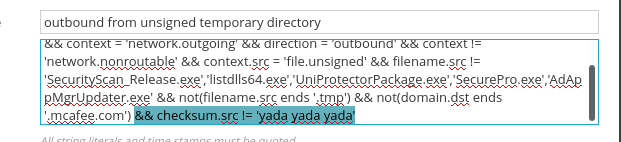
You can figure out this additional syntax by looking at the endpoint events triggering that app rule by querying for it in NetWitness:
(device.type = 'nwendpoint') AND (boc = 'outbound from unsigned temporary directory')
...and picking out the meta keys and values that will identify that specific application (checksum.src is probably a good one).
You would then add that as a != filter in the app rule:
The more specific and precise you can be to positively identify that application, the better.
Mr. Mongo
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2021-05-27 02:26 AM
I have gone through same problem, what I did
File which is unsigned , marked it as whitelisted
then I updated the APP rule and add one mode condition as below
context.src != 'file.whitelisted' && ......