- NetWitness Community
- Blog
- Bank on it with the Dridex Trojan
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
The Dridex Trojan is a strain of banking malware that began spreading in 20141. Its transport mechanism continues to be spam email, commonly referred to as malspam. It steals a victim's banking credentials in order to commit fraudulent financial transactions. Historically, Dridex relied on Microsoft Office macros to successfully infect a victim. A new campaign, however, reveals that it's now leveraging a Microsoft Word zero-day vulnerability (CVE-2017-0199) instead.
For the exploit to land, a user must open an attached Microsoft Word RTF (Rich Text Format) document. Contained within it is an embedded OLE2link object which executes winword.exe. That process sends a HTTP request to a remote server which retrieves a malicious .hta file, the payload2.
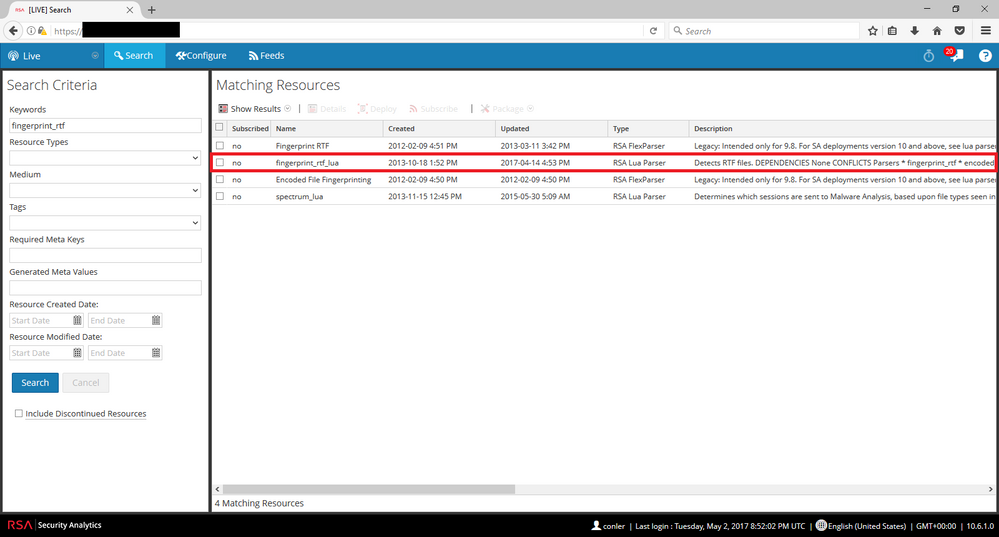
To enable detection of malicious RTF documents, users need to verify that their NetWitness installation has been configured with the:
-‘fingerprint_rtf_lua parser’ from RSA Live.
Once you have subscribed to and enabled this content in your environment, NetWitness will identify suspicious strings in the RTF header. Shown below is the parser flagging RTF traffic.
Thanks to Kevin Stear, Bill Motley, Angela Stranahan, and Christopher Ahearn for contributing to this threat advisory.
References:
1http://www.webopedia.com/TERM/D/dridex-malware.html
Additional reading:
http://thehackernews.com/2017/04/microsoft-word-dridex-trojan.html
https://isc.sans.edu/diary/22280
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0199
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- HYDRA Brute Force
- DDoS using BotNet Use Case
- A Closer Look at Advanced EPL (ESA) Through a Rule and its Components
- HTTPS Insecure Cipher Detection
- FirstWatch Threat Spotlight – Chaos RAT
- FirstWatch Threat Spotlight: HAVOC C2
- FirstWatch Threat Spotlight – BlueSky Ransomware
- Advanced HTTP and TLS Concepts (Video)
- Using NetWitness to Detect Command and Control: SILENTTRINITY C2
- FirstWatch Threat Spotlight – Remcos RAT
-
Announcements
64 -
Events
9 -
Features
12 -
Integrations
12 -
Resources
68 -
Tutorials
31 -
Use Cases
30 -
Videos
118