- NetWitness Community
- Blog
- Detecting a new Kazy variant using RSA Security Analytics
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Sometimes, it is really easy to spot the differences between regular and malicious network traffic. In this blog post, we will discuss how to detect a new Kazy based on the traffic originating from a couple of infected virtual machines in RSA FirstWatch Malware Analysis Systems.
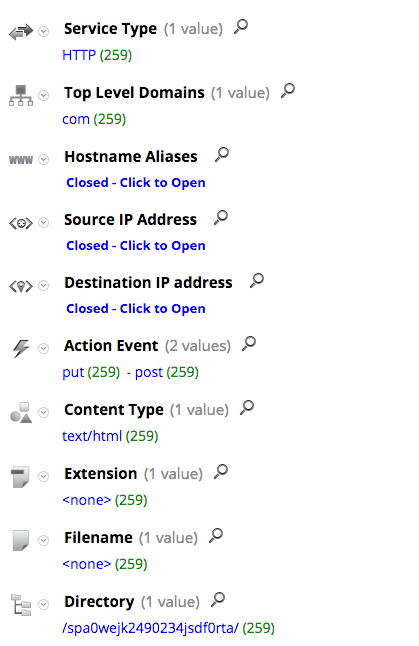
The screenshot below shows the HTTP traffic between the bots and their C2 domains:
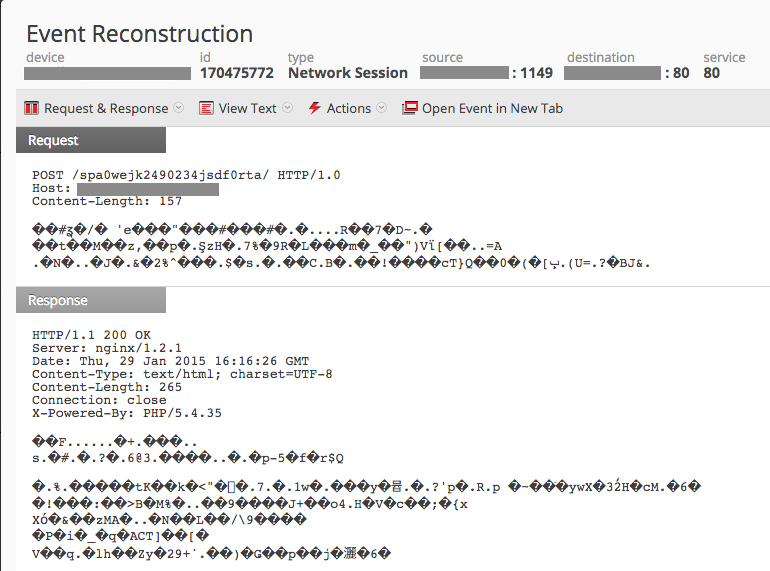
Using RSA Security Analytics to reconstruct one of those sessions we can see that the User Agent string is missing from the HTTP headers
Given all the network artifacts mentioned above and assuming the appropriate meta keys are enabled, an analyst can develop an app rule on RSA Security Analytics to detect the malicious traffic. The following query can be used:
directory = '/spa0wejk2490234jsdf0rta/' && action = 'put' && filename = '<none>' && client !exists
As of this writing, VirusTotal has a low detection rate of the sample under investigation.
Finally, all of the IOCs from those HTTP sessions were added to RSA FirstWatch Live feeds.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- A Closer Look at Advanced EPL (ESA) Through a Rule and its Components
- HTTPS Insecure Cipher Detection
- FirstWatch Threat Spotlight – Chaos RAT
- FirstWatch Threat Spotlight: HAVOC C2
- FirstWatch Threat Spotlight – BlueSky Ransomware
- Advanced HTTP and TLS Concepts (Video)
- Using NetWitness to Detect Command and Control: SILENTTRINITY C2
- FirstWatch Threat Spotlight – Remcos RAT
- FirstWatch Threat Spotlight: The LockBit Conundrum - A Glimpse into Ransomware Warfare
- Content Hygiene – Application Rule Alert Mapping Updates
-
Announcements
64 -
Events
9 -
Features
12 -
Integrations
12 -
Resources
68 -
Tutorials
31 -
Use Cases
32 -
Videos
118