- NetWitness Community
- Blog
- Detecting Laziok variants using RSA Security Analytics
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Last week, Symantec blogged about a new reconnaissance tool used in attacks that target the energy sector with a focus on the Middle East. Laziok, as called by Symantec, is an information stealer that collects configuration data about the compromised machines to help the attackers tailor their attacks against the victims. The collected data include:
- Computer name
- Installed software
- RAM size
- Hard disk size
- GPU details
- CPU details
- Antivirus software
According to the Symantec blog post, the campaign started in January which is about the same time that RSA FirstWatch Malware Analysis systems started processing some of those binaries.The screenshot below shows Laziok activity in our systems between mid-January and late-March:
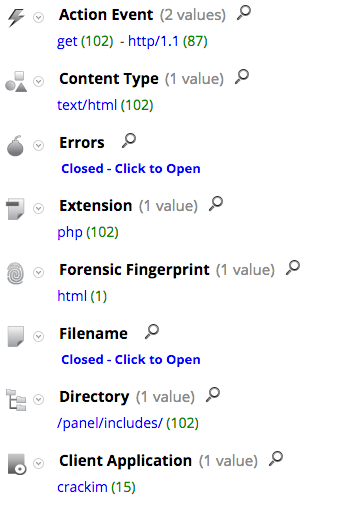
Digging deeper into the traffic between the infected machines and the C2 domains, there are some observations to make:
The User-Agent string is pretty unique but it is not present in all of the HTTP sessions so it can’t be used to detect all the HTTP GET requests to the C2 domains. However, the directory name and file extensions are unique and seem to be present in all of the related sessions.
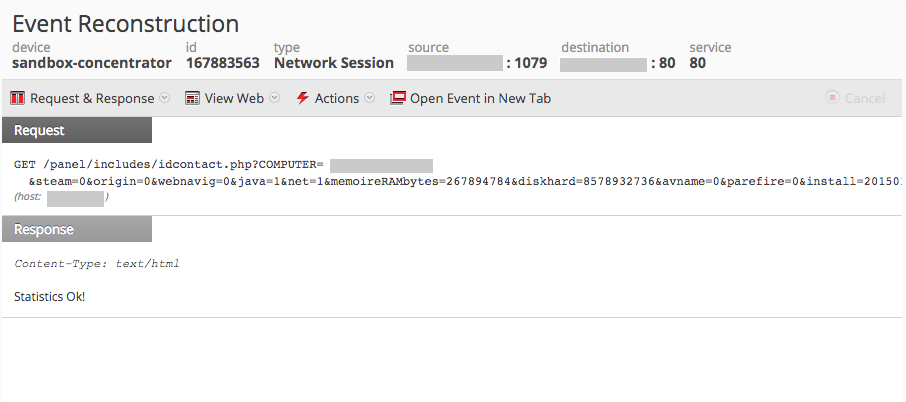
Reconstructing one of the sessions using RSA Security Analytics clearly shows the kind of information collected from the infected machine and sent to the C2 domain in the query string:
Given all the network artifacts mentioned above and assuming the appropriate meta keys are enabled, an analyst can develop an app rule on RSA Security Analytics to detect the malicious traffic. The following query can be used:
action = 'get' && directory = '/panel/includes/' && extension = 'php'
You can find VirusTotal scan results for one Laziok sample here.
All of the IOCs from those HTTP sessions were added to RSA FirstWatch Live feeds.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
- Netwitness Platform Integration with Amazon Elastic Kubernetes Service
- Netwitness Platform Integration with MS Azure Sentinel Incidents
- Netwitness Platform Integration with AWS Application Load Balancer Access logs
- The Sky Is Crying: The Wake of the 19 JUL 2024 CrowdStrike Content Update for Microsoft Windows and ...
- The Sky Is Crying: The Wake of the 19 JUL 2024 CrowdStrike Content Update for Microsoft Windows and ...
- New HotFix: Addresses Kernel Panic After Upgrading to 12.4.1
- Automation with NetWitness: Core and NetWitness APIs
- HYDRA Brute Force
- DDoS using BotNet Use Case
- A Closer Look at Advanced EPL (ESA) Through a Rule and its Components
-
Announcements
64 -
Events
12 -
Features
12 -
Integrations
15 -
Resources
68 -
Tutorials
32 -
Use Cases
31 -
Videos
119